2FA (Two Factor Authentication) or MFA, (Multi-Factor Authentication) should be used on every account where that is an option in order to add security to the account, here we will discuss the more common options and why some choices of 2FA are better than others.
We can divide 2FA types into a handful of categories:
SMS (Text Message link or code)
TOTP (Temporary One Time Passwords)
Software Tokens (Authenticator, Aegis, FreeOTP, AndOTP, Standard Notes)
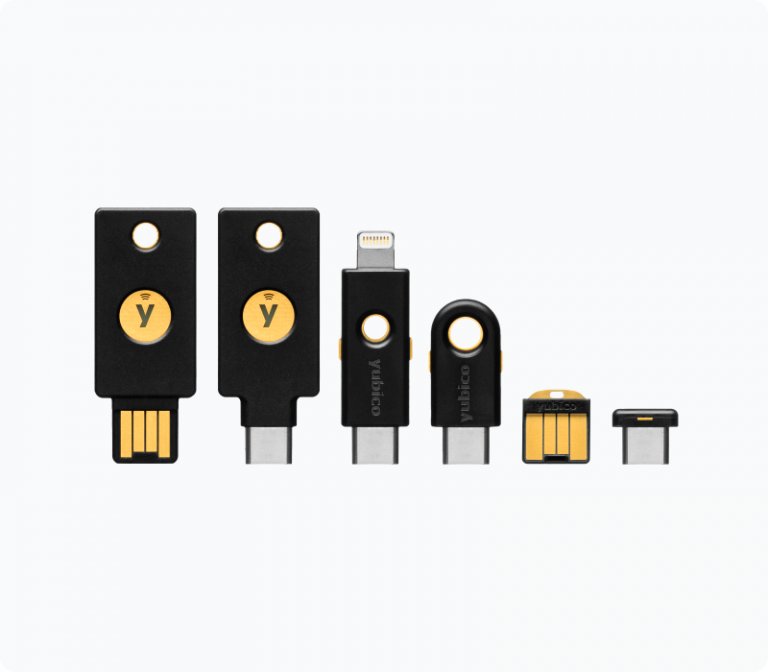
Hardware Tokens (Yubikey)
Recovery Codes (Seed Phrases)
Software Tokens are excellent 2FA, SMS is considered poor for privacy as this links your phone to your computer. While decreasing, another risk of SMS for 2FA is something called a SIM swap attack where an attacker gains access to your account through the hijacking of your SIM information and having the 2FA code sent to their phone in order to login or reset your account. This presents a serious security risk to your account. App generated codes (Software Tokens) are a much better choice to generate a TOTP, my top choices for these are:
Authenticator for your computer (Flatpak from Flathub.org version available on Linux only).
Aegis for your mobile device. (You can mix and match these, you don’t have to use only one; example, you could use Standard Notes for your X account on your computer, and also use Aegis on your phone to unlock the same X account) Use F-Droid to download Aegis to your Android device.
Ente Auth for both mobile device and desktop, works cross all platforms. End to end encrypted backups of your 2FA codes. Excellent option, and one of the few that works on both mobile and desktop platforms.
Standard Notes (paid tiers only) This allows you to use your Standard Notes account for 2FA codes which is my current strategy for 2FA software tokens, because I can access these from both my mobile device as well as from my desktop. However you can easily mix and match these services, so you don’t have to use just one 2FA app, but rather you can use as many as you like.
If App Generated codes or Hardware Tokens are not able to be used, avoid SMS and use email TOTP (you login to the site, and are required to grab a TOTP from an email sent to you and paste it into the site to gain access, usually this is a 6 digit number.
**Backup your Software Token application keys! (Best to store the backup code for each account in a separate method than your password manager for true 2FA)
Aegis on Android (Download from F-Droid store):
Ente Auth 2FA App works on Mobile and Desktop, on all platforms
Hardware Tokens are extremely robust for hardening your accounts, but not all accounts accept 2FA Hardware Tokens. This is a physical device such as a YubiKey that is required to be physically present in order to gain access to the account after giving your username/password. This ensures that even if someone steals or guesses your account credentials, they have to have access to the physical device in order to be successful at logging in. This means you also must have this present to access your stuff, I carry and use one every day.
They work like this- you login to say, your bank, something you want secured with the hardware token. You enter your username and password, and because you set up 2FA using the hardware token, you are challenged before entering the account. Simply plug in the hardware token (a YubiKey for example) to a USB port and when challenged at login, simply tap the Yubikey and it will auto-populate a key to grant access.
One YubiKey can get you into multiple accounts, not just one, and it is strongly recommended to always buy 2 or more of these in order to have a backup. You can clone up to 5 YubiKeys for a single account. These are fairly easy to setup with your accounts, look for 2FA or MFA under your settings menu in your account profile to pair the key with the account. There are other hardware tokens other than YubiKey also, and it’s possible to make your own using a USB drive, but I find YubiKey to be a much more reliable solution than anything else. Learn the technical aspect of a YubiKey here.
Recommended Yubikey 5 Series (Amazon)
Finally we have Recovery Codes, usually referred to as ‘Seed Phrases’ as an emergency recovery method should your physical Hardware Token be lost or destroyed. Most are 12 word, but you can see in this example below that 24 generated words are used. Anytime you use hardware tokens, it is your responsibility to have your recovery code saved in the event you lose your physical token, this helps guard against getting permanently locked out of your account.

Ascending through a complex field of crevassed snowfields on Mt Baker, WA